|
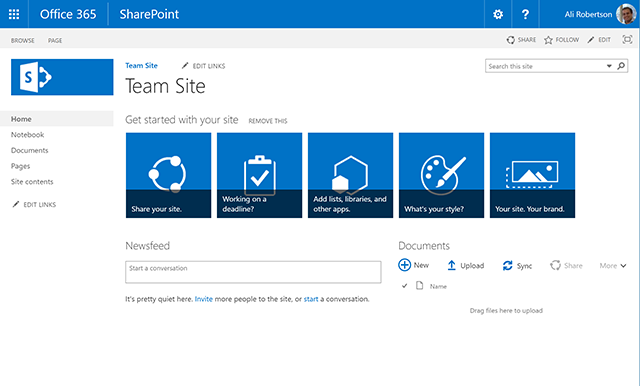
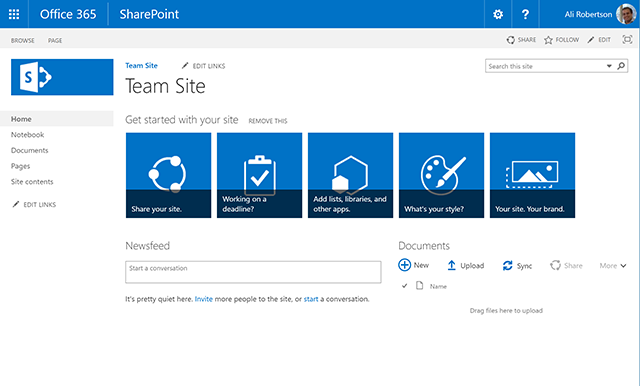
Microsoft SharePoint Server has a manual patching arrangement that is widely regarded as convoluted and complex.[{{Cite web |last=]Comments |first=Stefan Goßner-- 87 |date=2020-02-11 |title=SharePoint Patching Best Practices |url=https://blog.stefan-gossner.com/2020/02/11/sharepoint-patching-best-practices/ |access-date=2025-09-26 |website=Stefan Goßner |language=en-US}} Over the years, it has been subject to numerous critical security vulnerabilities, which are frequently exploited in the wild.[{{Cite web] |last=Unit 42 |date=2025-07-31 |title=Active Exploitation of Microsoft SharePoint Vulnerabilities: Threat Brief (Updated August 12) |url=https://unit42.paloaltonetworks.com/microsoft-sharepoint-cve-2025-49704-cve-2025-49706-cve-2025-53770/ |access-date=2025-09-26 |website=Unit 42 |language=en-US}} As a consequence, is no longer considered best practice to host SharePoint Server with public facing internet access. |
|
Microsoft SharePoint Server has a manual patching arrangement that is widely regarded as convoluted and complex.[{{Cite web |last=Goßner |first=Stefan |date=2020-02-11 |title=SharePoint Patching Best Practices |url=https://blog.stefan-gossner.com/2020/02/11/sharepoint-patching-best-practices/ |access-date=2025-09-26 |website=Stefan Goßner |language=en-US}}] Over the years, it has been subject to numerous critical security vulnerabilities, which are frequently exploited in the wild.[{{Cite web |date=2025-07-31 |title=Active Exploitation of Microsoft SharePoint Vulnerabilities: Threat Brief (Updated August 12) |url=https://unit42.paloaltonetworks.com/microsoft-sharepoint-cve-2025-49704-cve-2025-49706-cve-2025-53770/ |access-date=2025-09-26 |website=Unit 42 |language=en-US}}] As a consequence, is no longer considered best practice to host SharePoint Server with public facing internet access. |
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0